Cyber Insurance for the Healthcare Industry
Cyber Insurance for the Healthcare Industry

The healthcare industry has experienced many of the large and notable data breaches over the past decade.
As the industry has modernised its systems and processes to facilitate easy access to its customer’s most sensitive data, so too has it become exposed to internal and external threats putting that data at risk.
Beyond the mega breaches in the headline news though, it is often small and medium sized healthcare organisations facing a frequency of cyber incidents. These incidents can arise out of cyber-attacks or simply a human error, and can result in a myriad of different costs.
While the frequency, nature and severity of cyber incidents are constantly changing, patterns have in fact emerged for many industries which demonstrate key exposures and the corresponding controls necessary to mitigate them.
For the healthcare industry, the role cyber insurance can play in complimenting an enterprise risk management approach to cyber risk is increasingly clear.
Cyber Insurance By The Numbers
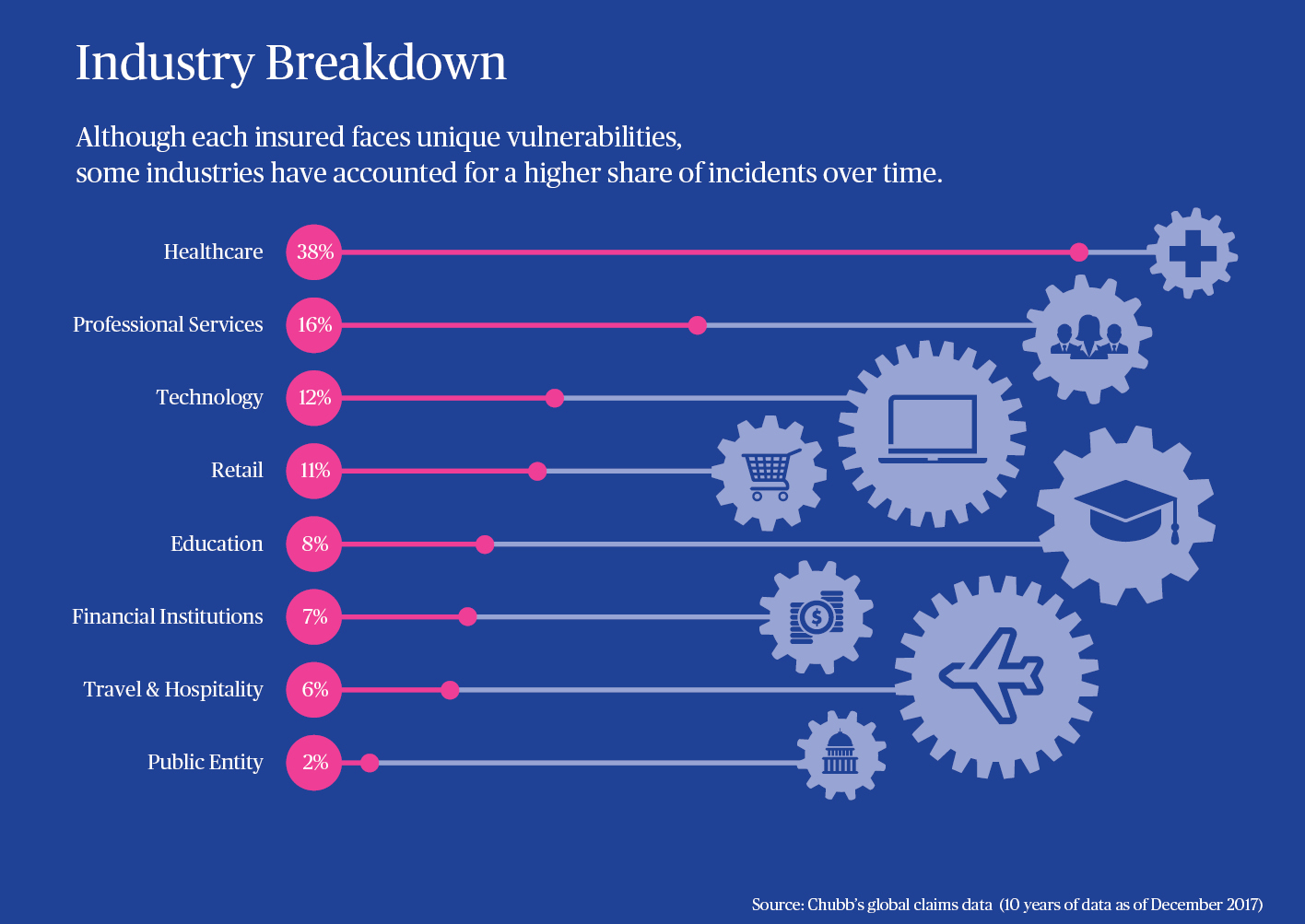
Based on an analysis of Chubb’s prior decade of claims experience, the healthcare industry made up 38% of all claims reported during that period. Further, the trend of incidents impacting the industry has continued into 2018 as the number of Chubb healthcare cyber-related incidents grew 13% over the past two years.
Internal Threats Rising
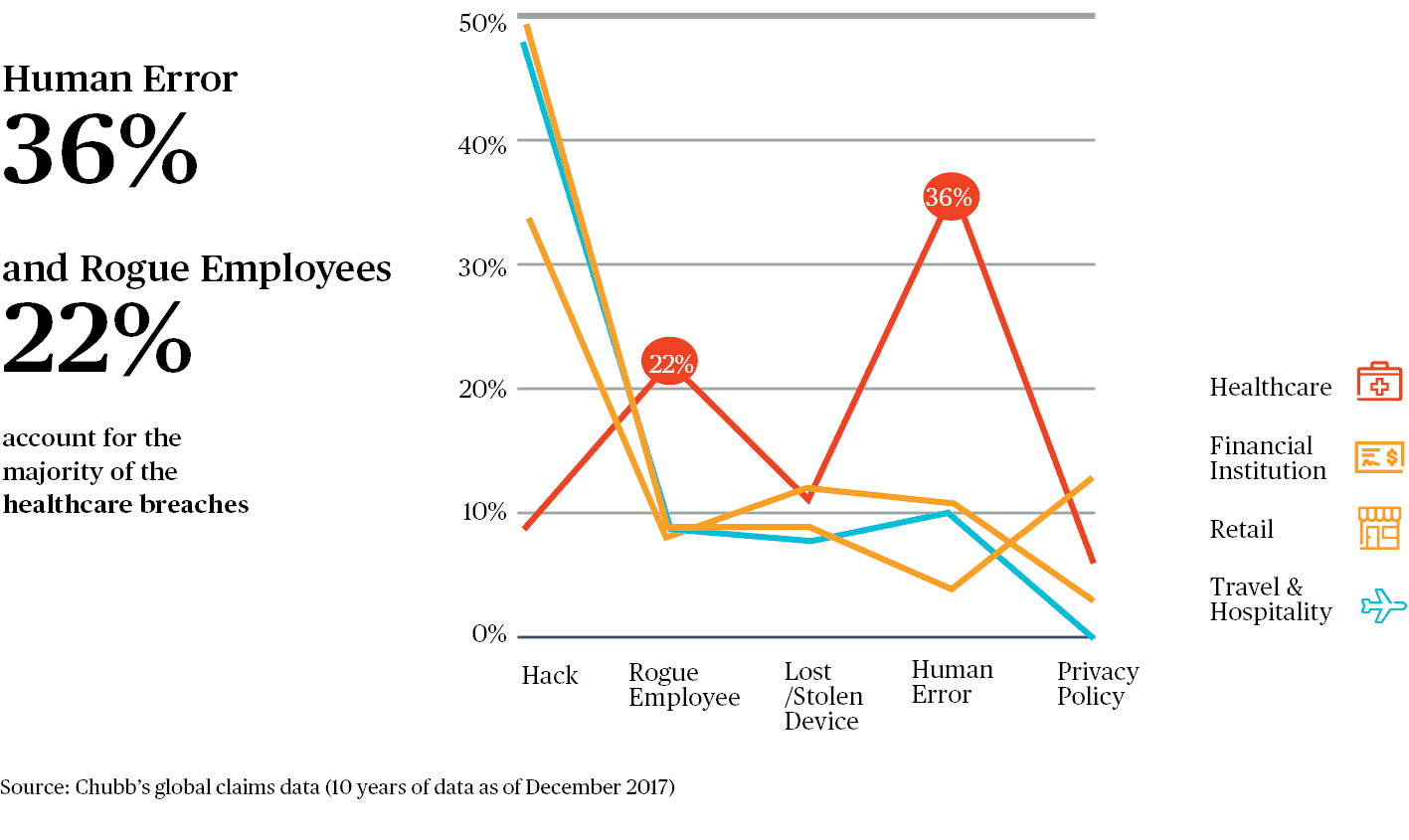
In terms of the make-up or “triggers” of cyber claims for the healthcare industry, Chubb’s experience in many ways debunks the belief that external bad actors hacking into an insured’s system are the predominate threat. In fact, just 9% of healthcare breaches have resulted from Hacks, which is the lowest of any industry we track.
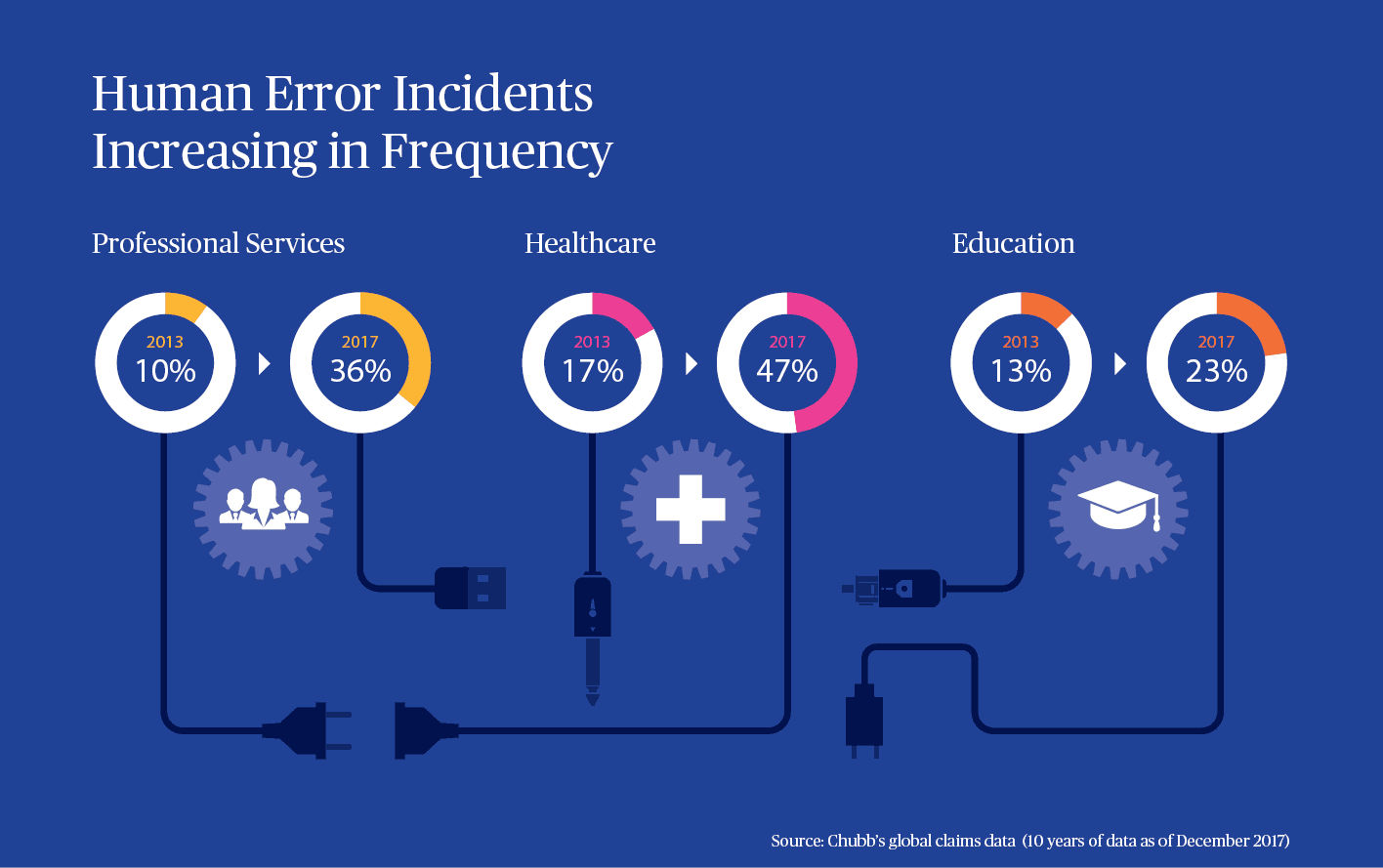
On the other hand, Human Errors and Rogue Employees have accounted for a combined 58% of all incidents. This experience suggests that while perimeter controls used to protect the organisation from malicious intrusion remain critical, other areas like employee training and internal access controls are equally important.
Ransomware On The Rise
Security Research firm Cybersecurity Ventures estimates global ransomware damage costs to be US $5 billion in 2017, with projections for damages to exceed US $11.5 billion annually by 2019.
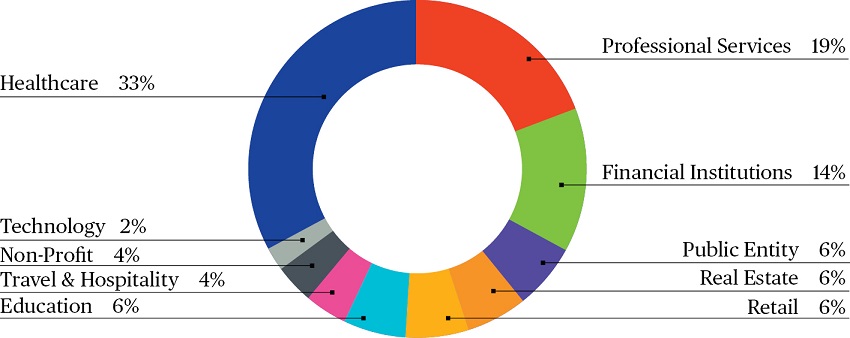
From the perspective of incidents handled by Chubb, the healthcare industry accounted for 33% of all ransomware attacks noticed, which is the most of any industry. These attacks have become increasingly destructive, and can have a significant impact on insureds in terms of the immediate costs incurred to mitigate and recover from the incident, as well as the lost income during the period of interruption.
Source: Chubb’s global claims data (10 years of data as of December 2017)
Key exposures & coverage
Key exposures
The following are some of the privacy and network security exposures faced by the healthcare industry:
- Data Breach - the theft of Personally Identifiable Information or Personal Health Information.
- Business Interruption - lost income and extra expenses arising out of malicious attacks or employee errors.
- Social Engineering - phishing emails or fake phone calls leading to the release of credentials or other sensitive information.
- Rogue Employees - malicious or even curious actors with access to patient data.
- Supply Chain - disruptions to your vendors like payment processors or Electronic Health Record portals.
Key coverages available
Cyber incidents can trigger immediate, direct costs as well as resulting liabilities. Some key elements of cover include:
- 24/7 Incident Response Expenses including Legal, IT Forensics, Public Relations and other Crisis Management experts available around the clock to assist in investigating and remediating cyber incidents.
- Business Interruption Loss due to a cyber-attack, network security failure, human errors, or programming errors.
- Data Asset Loss and restoration including decontamination and recovery for corrupted data.
- Network Extortion incidents like ransomware demands, where insurable by law.
- Liability arising from failure to maintain confidentiality of data or failure to prevent unauthorised access to your network.
- Regulatory investigations and resulting fines/penalties, where insurable by law.
A cyber claim scenario
What Chubb has paid
A hospital's computer system was the subject of a ransomware attack. While the attacker sought only $500, the attack essentially shut down the medical facility. The hospital incurred significant expenses attempting to restore the data from backup systems, and payroll, billing and imaging systems were inoperable during the period of restoration. With its systems completely corrupted, the hospital resorted to paper mode to chart and monitor patients. As a result of the attack, more than $700,000 was paid for forensics, data recovery, business interruption and crisis management costs.
Best practice controls
Implementing a holistic risk mitigation plan is the best defence against all types of cybersecurity breaches. Consider implementing the following seven measures to protect your organisation:
- Backup all systems routinely
- Providing annual employee trainings for both medical and non-medical staff on emerging cybersecurity threats and red flags to watch for
- Enable strong spam filters
- Invest in technologies that can scan and review emails for suspicious activity
- Limit access to privileged accounts
- Conduct regular penetration tests
- Improve password hygiene
No part of this article may be reproduced in any written, electronic, recording, or printed form without written permission of Chubb.
@2022 Chubb. The contents of this document are for informative purposes only and do not constitute advice. Please review the full terms, conditions and exclusions of our policies to consider whether they are right for you. Coverage may be underwritten by one or more Chubb companies or our network partners. Not all coverages and services are available in all countries and territories. Chubb® and its respective logos, and Chubb. Insured.SM are protected trademarks of Chubb.
Have a question or need more information?
Leave your contact details and our representatives will get in touch with you.